When you think about cybersecurity, your mind might jump to firewalls, antivirus software or the latest security tools. But let’s take a step back—what about your team? The reality is that even with the best technology, your business is only as secure as the people who use it every day.
Here’s the thing: cybercriminals are intelligent. They know that targeting employees is often the easiest way into your business. And the consequences? They can range from data breaches to financial losses and a lot of sleepless nights.
So, let’s break this down. What threats should you be worried about, and how can regular training protect your team and business?
Common cyberthreats that specifically target employees
These are some of the main ways attackers try to trick your team:
- Social engineering
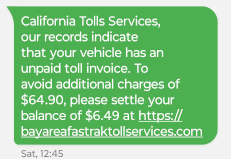
This is a tactic in almost all cybercriminal playbooks. Attackers rely on manipulation, posing as trusted individuals or creating urgency to fool employees into sharing confidential data or granting access. It’s about exploiting trust and human behavior rather than technology. - Phishing
A popular form of social engineering, phishing involves deceptive emails or messages that look official but aim to steal sensitive information or prompt clicks on harmful links. - Malware
Malware refers to malicious software designed to infiltrate systems and steal data, corrupt files or disrupt operations. It often enters through unintentional downloads or unsafe websites, putting your data and functionality at risk. - Ransomware
A specific kind of malware, ransomware, encrypts files and demands payment to unlock them. It’s one of the most financially damaging attacks, holding businesses hostage until a hefty ransom is paid.
Employee cyber awareness training and its benefits
You wouldn’t let someone drive your car without knowing the rules of the road, right? The same logic applies here. Cyber awareness training equips your team with the knowledge to spot and stop threats before they escalate. It’s about turning your employees from potential targets into your first line of defense.
The benefits of regular employee cyber awareness training are:
- Fewer data breaches
Well-trained employees are less likely to fall for phishing or other scams, which lowers the chance of a data breach. - Stronger compliance
Many industries require security training to meet legal standards. By staying compliant, you avoid potential fines and build trust with partners. - Better reputation
Showing a commitment to security through regular training shows clients and customers that you take data protection seriously. - Faster responses
When employees know how to spot and report issues quickly, the response to any threat is faster and more effective, minimizing potential damage. - Reduced insider threats
Educated employees understand the risks, minimizing both accidental and intentional insider threats. - Cost savings
Data breaches come with huge costs, from legal fees to loss of customer trust. Training can lessen the chances of cyber incidents and save your company money in the long run.
So, where do you start?
Start with a solid cybersecurity program. This isn’t a one-and-done deal. It’s ongoing. Your team needs to stay updated on new threats and best practices. And it’s not just about sitting through a boring presentation. Make it engaging, practical and relevant to their daily roles.
By investing in your team, you’re not just boosting their confidence—you’re safeguarding your business. And in a world where cyberthreats evolve faster than ever, that’s a win you can count on.