When most people picture cybercrime, they think of giant corporations, big-city hospitals, or government agencies getting hit by hackers.
But in 2025, that picture is wrong.
Across California and the nation, small and rural organizations are increasingly in the crosshairs—manufacturers, farms, clinics, local governments, food processors, retail shops, and professional offices. In many cases, these attacks are causing weeks of downtime, permanent data loss, and six-figure recovery bills.
For businesses in places like Tuolumne County and the broader Mother Lode, cybersecurity is no longer a “big city problem.” It’s a business survival problem.
This post looks at:
- Why rural businesses are now prime targets
- Common myths that keep small businesses exposed
- Real examples of cyber incidents impacting smaller and rural California organizations
- What “proactive cybersecurity hygiene” actually means in day-to-day operations
- How NTELogic helps local businesses improve their security culture and resilience
“We’re Too Small to Be a Target” – The Most Expensive Myth in Rural Business
Attackers don’t care about your ZIP code or how many people are in your town. They care about three things:
- How easy you are to compromise
- How quickly you’ll pay to get back online
- How quietly they can move on to the next victim
Recent research shows just how wrong the “only big companies get hit” myth really is:
- Roughly 46% of all cyber breaches now impact organizations with fewer than 1,000 employees.
- An estimated 43% of cyberattacks in 2023 targeted small businesses specifically.
- The FBI’s 2024 Internet Crime Report logged more than 859,000 cybercrime complaints with reported losses over $16 billion, a 33% increase over the prior year.
And small businesses are paying a heavy price. The U.S. Small Business Administration notes that cybercrimes against the small business community cost an estimated $2.9 billion in 2023 alone.
For a local dental office, insurance agency, or construction firm, that kind of incident isn’t an inconvenience, it can threaten the business itself.
Why Rural Businesses Are Especially Attractive Targets
Rural communities like Tuolumne County, Calaveras County, and other parts of the Central Valley and Mother Lode share some common realities that cybercriminals quietly exploit:
1. Limited in-house IT staff
Most rural businesses don’t have a full-time cybersecurity team—or even a full-time IT person. Technology tends to be managed by:
- An office manager “who’s good with computers”
- A business owner juggling many roles
- A remote IT provider who only gets called when something breaks
That means critical tasks like patching, log review, MFA rollout, or staff training often get pushed aside.
2. Older systems and specialized line-of-business apps
Agriculture, healthcare, manufacturing, and local government often run older software and specialized systems—from feed and dairy management platforms to legacy accounting software and controllers for pumps, gates, and machinery.
These systems are:
- Harder to patch or update
- Sometimes no longer supported by the vendor
- Often exposed to the network in risky ways
Attackers love that combination.
3. Connectivity challenges and “workarounds”
Rural internet constraints can lead to creative, but risky solutions:
- Remote access tools left open to “make it easier to support sites”
- VPNs or port forwarding set up once and never revisited
- Shared admin passwords used on multiple systems
These shortcuts are convenient for daily work but create a wide attack surface.
4. Heavy dependence on uptime
Many rural operations run 24/7 – dairies, farms, critical infrastructure, clinics, and hospitality. Shutting down even for a day can mean:
- Spoiled product
- Missed harvest windows
- Lost bookings and revenue
- Disrupted services to the community
Attackers know that organizations under severe uptime pressure are more likely to pay ransom quickly.
Real-World Cyber Incidents in Smaller & Rural California Communities
You don’t have to look to Silicon Valley or Los Angeles to see the damage cybercrime can cause.
Here are a few examples from smaller or rural California organizations:
A California agriculture business crippled by ransomware
A California-based agricultural business suffered a serious ransomware attack while working with a previous IT provider. The attack disrupted operations so badly that they had to rebuild their network and systems with help from a new IT security partner.
This was not a global corporation, it was an agriculture company, the kind of business you might find in any Central Valley or foothills community.
Grass Valley and Shafter: small cities, big cyber impacts
The City of Grass Valley, a town of around 13,000 people, disclosed that its systems had been compromised by ransomware, with attackers threatening to publish stolen city data if ransom wasn’t paid.
Similarly, the City of Shafter, a small agricultural city in Kern County, reported a ransomware incident that froze and locked its IT system, disrupting city services and forcing City Hall to close while the incident was investigated.
While these are municipalities rather than private companies, the lesson is the same:
If a small city government can be shut down by ransomware, so can a local business running similar technology and facing similar resource constraints.
Healthcare facilities serving local communities
Healthcare organizations that serve regional and rural populations have also been hit hard:
- Granite Wellness Centers, which operates in Northern California communities, discovered a ransomware attack that exposed the information of approximately 15,600 patients, including health and insurance data.
- Mission Community Hospital in Panorama City, California, has been the subject of multiple reports and legal filings following a 2023 ransomware attack in which attackers claimed to steal roughly 2.5 TB of data, including imaging records, employee information, and financial reports.
Again, the pattern is clear: cybercriminals are not just going after national hospital chains, they’re targeting community-focused organizations that often lack enterprise-grade budgets or staffing.
If attacks like these can hit rural or regional organizations in California, they can absolutely hit a professional office, retail shop, clinic, or ag operation in Tuolumne County.
What Proactive Cybersecurity Hygiene Looks Like (In Plain English)
“Cybersecurity hygiene” sounds abstract, but in practice it’s a collection of very concrete habits, tools, and decisions.
Here’s what that looks like for a rural business that wants to stay ahead of threats.
1. Know what you have (and where it is)
You can’t protect what you don’t know about.
- Maintain an inventory of devices (PCs, laptops, servers, tablets, phones, network gear).
- Track software and line-of-business apps, including older systems that are still critical.
- Document where your data lives (local servers, cloud apps, USB drives, backup systems, third-party services).
2. Keep systems patched and protected
Most attacks still succeed by exploiting known, unpatched vulnerabilities.
- Enable automatic updates where possible.
- Use managed endpoint protection (EDR/MDR) rather than basic consumer antivirus.
- Regularly review and update firewall and remote access settings.
3. Lock down identities and access
Human logins are often the weakest link.
- Turn on multi-factor authentication (MFA) for email, remote access, and cloud apps wherever possible.
- Use unique, strong passwords stored in a password manager instead of reusing the same password everywhere.
- Limit admin access, only give high-level privileges to people who truly need them.
4. Make backup and recovery non-negotiable
A backup you think is working is almost as dangerous as having no backup at all.
- Use managed, monitored backups with both local and cloud copies where possible (especially important with unreliable rural internet).
- Ensure backups are encrypted and protected from ransomware (offline or immutable copies).
- Test restores regularly so you know how long it will take to get systems back up.
5. Train your team – over and over
Today’s phishing scams and phone-based social engineering (“vishing”) are sophisticated. Attackers use:
- Look-alike domains
- Fake Microsoft or bank logins
- Phone calls pretending to be “IT support”
Regular security awareness training and simulated phishing campaigns help staff recognize and report attacks instead of falling for them.
6. Plan for the “when,” not just the “if”
Every rural business should have a simple, clear incident response plan:
- Who gets called first (internal and external)?
- How do you isolate infected systems?
- How do you communicate with customers or patients if systems are down?
- Who handles law enforcement notifications, breach notifications, and cyber insurance claims?
Even a 2–3 page playbook written in plain language is better than scrambling after the fact.
Building a Security Culture in a Rural Business
Technology is only half the story. In smaller communities, culture is often the deciding factor between resilience and disaster.
A strong security culture in a rural business looks like:
- Leaders talking about cybersecurity the way they talk about safety, quality, or customer service.
- Employees feeling comfortable speaking up if something looks suspicious.
- Regular, short “toolbox talks” or lunch-and-learns on topics like phishing, passwords, and safe remote work.
- Clear, written policies for acceptable use, remote access, and handling sensitive data.
- Security being considered during business decisions, not bolted on afterwards (for example, when adding a new cloud system or remote site).
In places like Tuolumne County, where many people know each other personally, that culture can spread quickly, especially when it’s framed not as fear, but as taking care of employees, customers, and the community.
How NTELogic Helps Rural Businesses Strengthen Cybersecurity
NTELogic was built in and for communities like the Mother Lode and Central Valley. We understand:
- Unreliable rural internet and the need for local + cloud strategies
- The specialized software used by agriculture, dairy, and other rural operations
- The realities of small IT budgets and lean staffing
- The importance of keeping operations running 24/7
Here’s how we support local businesses in improving their security posture and culture:
1. Managed endpoint protection and monitoring
We deploy and manage enterprise-grade endpoint detection and response (EDR) and remote monitoring to:
- Detect ransomware and malware behavior early
- Isolate compromised devices
- Keep systems patched and up to date
- Provide visibility across laptops, desktops, and servers
2. Managed backup and disaster recovery
Our NTELogic Managed Backup Service is designed with rural realities in mind:
- Flexible selection of which data and applications to protect
- Support for applications that store data in non-standard locations (including common ag and dairy software)
- Encrypted backups with options for both local appliances and cloud storage
- Regular monitoring, testing, and support when a restore is needed
This combination helps minimize downtime and makes it much easier to say “no” to ransom demands.
3. Secure email and identity protection
Because so many attacks start in the inbox, we help local businesses:
- Harden Microsoft 365 and hosted email with advanced email protection
- Implement MFA and conditional access where supported
- Set up and manage DKIM, SPF, and DMARC to reduce spoofing and improve email trust
- Provide guidance on identity-based licensing and changes in Microsoft’s Office and M365 ecosystem
4. Security awareness and culture programs
Technology alone won’t fix human risk, so we offer:
- Ongoing cybersecurity awareness training for employees
- Phishing simulations tailored to common scams hitting local businesses
- Simple, rural-friendly policies and quick-reference guides
- Executive and owner briefings to align security with business priorities
5. Business continuity and incident planning
Drawing on decades of experience in business continuity, emergency management, and IT, we can help you:
- Identify critical systems and data
- Map out dependencies across sites and vendors
- Build and document incident response and recovery plans
- Run tabletop exercises so your team knows how to react under pressure
Bringing Big-City Cybersecurity to Small-Town Businesses
Cybercrime is no longer a distant, abstract risk reserved for Fortune 500 companies. It’s already affecting towns like Grass Valley and Shafter, regional healthcare providers, and agriculture businesses that look a lot like the operations up and down Highway 49 and 99.
For rural businesses in Tuolumne County and the surrounding region, the choice isn’t whether to “do cybersecurity” or not. The choice is whether to approach it reactively after an incident, or proactively as part of how you run your business.
If you’d like help:
- Assessing where your biggest risks actually are
- Building a realistic, affordable cybersecurity roadmap
- Putting managed protection, backup, and training in place
- Or simply translating all this jargon into a plan your team can follow
NTELogic is here in your backyard, not a faceless call center three time zones away.










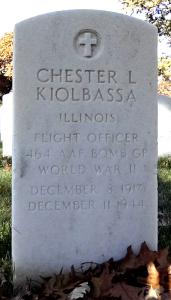
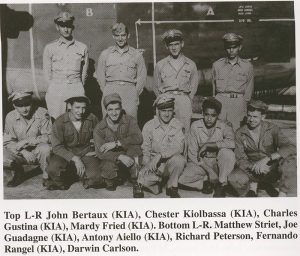 when the skies were filled with danger and uncertainty. In the early morning hours of December 11, 1944, somewhere over Austria, his plane was shot down by enemy fire. Recorded in the Missing Air Crew Report was a statement from one of only two surviving crew members who said he saw the pilot and co-pilot (Uncle Chester) struggling to control the aircraft as the rest of the crew bailed out. Chester was only 22 years old when he gave his life in service to our country.
when the skies were filled with danger and uncertainty. In the early morning hours of December 11, 1944, somewhere over Austria, his plane was shot down by enemy fire. Recorded in the Missing Air Crew Report was a statement from one of only two surviving crew members who said he saw the pilot and co-pilot (Uncle Chester) struggling to control the aircraft as the rest of the crew bailed out. Chester was only 22 years old when he gave his life in service to our country.