You invested in the latest security software and even hired a great IT team. However, one misstep by an unsuspecting employee and a wrong click on a malicious link later, you are staring at a costly breach that threatens to jeopardize the future of your business.
Scary right? But it doesn’t have to be your reality!
The best way to secure your business isn’t just through firewalls or antivirus alone. Your employees also play an equally critical role in protecting your business. When employees lack adequate security training, they can become easy targets and fall prey to phishing scams or malicious malware.
That’s where your role as a business leader becomes crucial. You have the power to steer your team to embrace a security-first culture. In this blog, we will show you how prioritizing continuous training and support can transform your workforce into your greatest cybersecurity ally.
Why prioritize employee cyber awareness training?
Your employees are like the guardians of your castle. But they must be equipped with the weapons and skills they need to defend you from your enemies.
Let’s explore how training empowers your employees to:
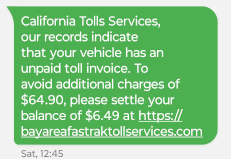
Identify and avoid phishing attacks: When employees have proper security training, they can spot the red flags in a suspicious email. They recognize the telltale signs like unfamiliar sender addresses, grammar errors or unexpected attachments. They also become more cautious when they see a suspicious link. This helps businesses like yours reduce risks by avoiding costly mistakes.
Practice good password hygiene: Training ensures your employees know why good password hygiene is so important and necessary to reduce cyber risks. They also learn the value of creating strong and unique passwords, how to use a password manager and the importance of employee accountability.
Understand social engineering tactics: Untrained employees can easily fall prey to manipulative behaviors. Training helps them spot if someone is impersonating a trusted individual to extract sensitive information. It also equips them with the knowledge of how to question and verify identities when they suspect someone is impersonating a trusted authority.
Handle data securely: A crucial aspect of employee cyber awareness training is educating your team on how to handle data securely. When employees are well-trained and get regular refreshers on storage practices and updated encryption methods, it can greatly reduce cyber risks.
Report suspicious activity: Effective training empowers employees to identify and report suspicious activities, such as unauthorized access attempts or unusual system behavior. Trained employees feel confident and are more likely to report issues, thereby preventing small issues from snowballing into serious security threats.
The importance of leadership in cybersecurity
As the leader of your team, you have the power to set the right tone and practices to ensure your business is protected. When employees see your commitment to improving cyber hygiene, they’re more likely to feel inspired and follow suit.
Here is how you can make a difference:
Communication is key: Make it clear to your employees that you take cybersecurity seriously. Ensure your workforce understands all security protocols, and explain all key information in an easy-to-understand and relatable language. Make communication a two-way street by encouraging your team to come back with feedback or questions so you can identify any gaps in the training.
Set the standard: Instill a culture of cybersecurity best practices into every aspect of your business—whether it’s investing in software, third-party vendors or managing policies related to remote work and data management. Doing so will help you set the right foundation and culture, reinforcing the importance of staying vigilant and proactive.
Empower your employees: Ensure your employees have access to password managers, multi-factor authentication and regular cyber awareness training. By empowering your employees, you can be confident that they will play an active role in protecting your business from threats.
Promote continuous training and learning: Building an organization with a security-first culture requires time, dedication and continuous effort. Your employee training and learning, therefore, will have to be a continuous process, not an annual event. By investing in ongoing training and learning, you can ensure your employees are updated on the latest threats and security practices.
Embrace security as a shared responsibility: Promote a culture where accountability is cherished as a shared value and every employee understands their role in protecting the business. When your team truly recognizes how their actions can impact the business, they can take more ownership and play an active role in securing your assets.
Wondering how to get started?
A boring, check-the-box training won’t cut it. Your team needs practical training that helps them stay ahead of evolving cyberthreats.
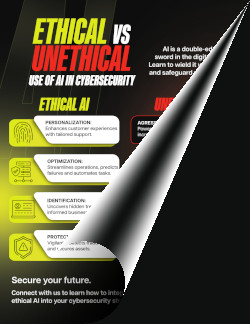
But don’t be overwhelmed! You don’t have to figure it out alone. We can help. As your trusted IT service provider, we can help you create comprehensive training tailored to your team’s needs.