It’s easy to take email for granted because it’s been around for so long that you expect it to always work. However, like other vital business functions, having the best email service can improve your operations by helping you close deals and retain valuable customers.
As well, without a reliable provider, you might be more likely to suffer a disastrous data breach through email. Recent figures show that the average cost of breaches for small and medium-sized businesses is $2.98 million.
To get the most out of your email communications, review the top features your organization must have when choosing (or switching to) an email provider.
Key Takeaways:
- Your email service can improve or impair the quality of your business.
- Use an email service that offers sufficient storage, gives you a custom domain, and integrates with your other business applications.
- Your email service should offer exceptional security, reliable backup and recovery, archiving capabilities, and round-the-clock support.
More Reasons Why You Need To Find the Best Email Service
If you’re still not convinced that you need to invest in the best email service you can get, keep the following five points in mind:
- Over half of the world’s population uses email to communicate.
- Over three-quarters of marketers have seen an increase in email engagement.
- Customers prefer brand communications through email.
- Business professionals prefer to communicate through email.
- Email marketing has one of the highest returns on investment of all marketing techniques.
Since email remains vital, you don’t want problems with attachments, campaigns, or spam to become issues that interrupt your activities. Take full advantage of all email can offer by selecting a service with the following features.
1. Abundant Storage Capacity
When you’re serious about client outreach, you’re going to be emailing a lot. The best email service will provide more storage than you can use.
As images and video become more important to communication, you don’t want overly restrictive limits on file sizes to get in the way of getting your message across. Check that available plans have sufficient storage for your company’s needs.
2. Custom Domain Names
Messages from the domain of a free email provider like Gmail or Yahoo do not look professional, and recipients may send them straight to the Spam folder. One of the best email service features is the ability to use one of your websites as the domain for your email.
Custom domains demonstrate that you’re serious about your business. Plus, personalized domains give you another way to get your branding out there.
3. Integration With Productivity Apps
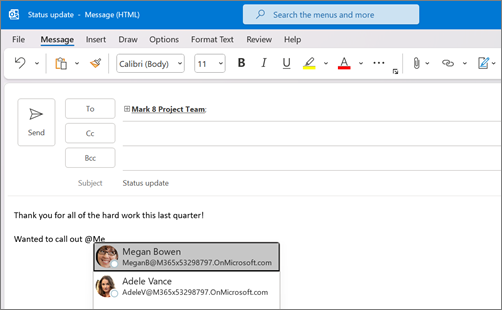
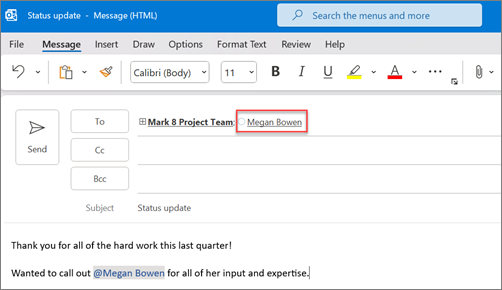
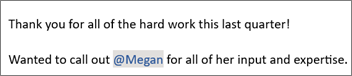
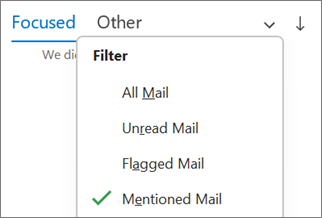
A wealth of information flows through your email communications. Your team needs to access and transfer that information into your other software that facilitates your operations, such as Microsoft 365.
Minutes your team spends toggling between apps for data entry turn into hours of lost time that your people could use for more important activities. That’s why the best email service integrates with your communications tools for seamless collaboration and productivity.
One dashboard lets workers handle email, voice calls, video conferencing, and chat. Putting all of your communications tools into one interface saves time and alleviates the frustration of constantly switching screens.
4. Full-Time Security
Email still remains a heavy conduit for cyberattacks and threats. The best email service providers will protect you from data breaches with secure encryption, whether your messages are at rest or in transit.
Also, continual reports about system hacks show that passwords can be the easiest thing to steal. This means security should start at login.
A provider with two-factor authentication requires more than a password to enter an account. The system verifies users through another device, so your precious data remains guarded behind another wall of protection.
Security services can scan your email traffic to prevent confidential information from falling into the wrong hands. Language-powered detection checks for irregularities and potential threats to stop malicious attacks.
5. Reliable Backup
Personal and professional email users have become more reliant on the cloud. That cloud is only as good as the provider maintaining it, though. You may just assume that your information will always be there when you need it, until it isn’t.
The best email service protects you from data loss with server redundancies so that outages, malfunctions, and disasters do not erase valuable information.
6. Email Archiving
You need to be able to access your emails later for numerous reasons. Quick message retrieval can resolve service issues and legal complications.
For example, when a worker makes an egregious mistake, that person may take great pains to erase the trail of what happened. Archiving keeps all information that occurs on your servers and gives you full access to it.
Further, companies in industries with strict regulations can have the reassurance that they have the necessary emails on hand to meet compliance standards. If a legal issue arises and electronic discovery is necessary, your legal team doesn’t have to worry about losing precious data or evidence.
7. Customer Support
You might think, “What could go wrong with email?” However, a little downtime on your server can snowball into a mountain of problems, whether you’re dealing with a technological issue, security threat, or human error.
With the best email service providers, you have constant support. Lesser providers might only have customer assistance as an add-on feature. Other services limit how many calls you can make for help. When you have any issues, you should be able to count on world-class support at all times.
Additionally, you can’t get the most out of your productivity tools without someone guiding you on which options meet your unique needs and showing you how to use them. Support services should also offer complimentary expert migration and onboarding.
Your Source for the Best Email Service Features
The quality of your business cloud applications can be the deciding factor in the success of your organization. To ensure you’re using the best email service, contact NTELogic for solutions that maximize your productivity and minimize your headaches.